Can my boss track my online activity with my personal computer thru the WiFi?
#1
Can my boss track my online activity with my personal computer thru the WiFi?
Just started my new job, it's LONNNNG hours. I've been casually browsing as well as doing the training, and I think my boss knows about it, or I'm being paranoid.
I don't see how he'd be able to tell, b.c it's my personal computer, I'm just using the WiFi.
Does anyone with experience with that shit know?
I can't find a conclusive answer anywhere!
I don't see how he'd be able to tell, b.c it's my personal computer, I'm just using the WiFi.
Does anyone with experience with that shit know?
I can't find a conclusive answer anywhere!
#2
It's possible. But if there are a lot of clients logging on to the router, then usually they won't check. It's the client computers that are hardwired that they check the most. They are constantly monitored.
#7
Just started my new job, it's LONNNNG hours. I've been casually browsing as well as doing the training, and I think my boss knows about it, or I'm being paranoid.
I don't see how he'd be able to tell, b.c it's my personal computer, I'm just using the WiFi.
Does anyone with experience with that shit know?
I can't find a conclusive answer anywhere!
I don't see how he'd be able to tell, b.c it's my personal computer, I'm just using the WiFi.
Does anyone with experience with that shit know?
I can't find a conclusive answer anywhere!
Trending Topics
#10
 it is possible for them to track most communication between your personal computer and the Internet if you are on their network. Whether or not they do it...who knows. The simple (and safe) answer is to stop doing what you shouldn't be doing
it is possible for them to track most communication between your personal computer and the Internet if you are on their network. Whether or not they do it...who knows. The simple (and safe) answer is to stop doing what you shouldn't be doing  .
.
#11
If it's about control, then they would give you a certain car to drive. I've been in sales for 20 years, it's about what's most economical for the company.
#13
Seems then it would be cheaper for a company not to buy computers or have an IT dept, and instead require their employees to provide for their own computing needs????
#15

#16
#17
A computer is a tool needed for you to perform your job, it cost what $500. A car cost $20k plus maintenance for high miles put on it, plus the have to pay property taxes at a higher rate and cover you with about 500,000 worth on insurance.
#18
and if you want to prevent what you are doing to be seen then install a proxy server on your home machine and then SSH tunnel there and now since it is secure all they will see is you connecting to your home machine. (not an easy setup though)
#20
To add one more viewpoint to this, if you were to use your own computer, when you left, so would all the information/data you've created.
#23
Sounds like the best and most demanding boss is one that looks at you in the mirror.
#24
#25
I get paid a lot of money to root out people who do exactly that.
May companies prohibit employees from using their own gear, including USB drives, IPods, etc. in machines for this very purpose. Violation of this policy may be a terminable offense.
In the olden days (geez did I just say that?) IT departments would physically remove the floppy drives. Now they can either disable the USB or use software that only allows specific PID/VID and serial number USB devices on company machines. FW is a different ball of wax. I know work environments where cell phones with cameras are prohibited, and I know of (seen myself) people who have tried to steal proprietary formulas, data, documents, information, etc by almost any means you can come up with, and then some.
May companies prohibit employees from using their own gear, including USB drives, IPods, etc. in machines for this very purpose. Violation of this policy may be a terminable offense.
In the olden days (geez did I just say that?) IT departments would physically remove the floppy drives. Now they can either disable the USB or use software that only allows specific PID/VID and serial number USB devices on company machines. FW is a different ball of wax. I know work environments where cell phones with cameras are prohibited, and I know of (seen myself) people who have tried to steal proprietary formulas, data, documents, information, etc by almost any means you can come up with, and then some.
#26
^ Does your investigation include old, legacy mainframes from the 1960's (punchcard era) that's been modified and moded a zillion times with a zillion records with more leaks that a 1949 Ford truck?
If not, I'm safe for tonight.
If not, I'm safe for tonight.
#28
Otherwise, you will be hard pressed to succeed in subverting big brother.
#30
If you connect to the wifi at my home or work, I can tell you what your grandmother is doing at her house right now. I can tunnel right back into your PC like a wide open book and take anything I want.
#31
ive been doing this at work for about... 6-7 yrs now. kinda obvious suggestion is to name your PC something random and unidentifiable. I mean don't have your username or last name there. now that would be REALLY dumb.
#32
Trolling Canuckistan
Joined: Oct 2005
Posts: 10,453
Likes: 811
From: 100 Legends Way, Boston, MA 02114
#34
intelligentsia
Joined: Nov 2003
Posts: 4,376
Likes: 0
From: Land of cheap vodka, hot girls, and great nightlife
If your using wifi try using this http://hotspotshield.com/ . I use it all the time at school so I can torrent and look at porn without my university knowing.
#36
But as an IT person, you cannot guarantee that the person is keeping their machine up to date with AV and patches opening up your network to viruses and other malware.
and if you want to prevent what you are doing to be seen then install a proxy server on your home machine and then SSH tunnel there and now since it is secure all they will see is you connecting to your home machine. (not an easy setup though)
and if you want to prevent what you are doing to be seen then install a proxy server on your home machine and then SSH tunnel there and now since it is secure all they will see is you connecting to your home machine. (not an easy setup though)
#37
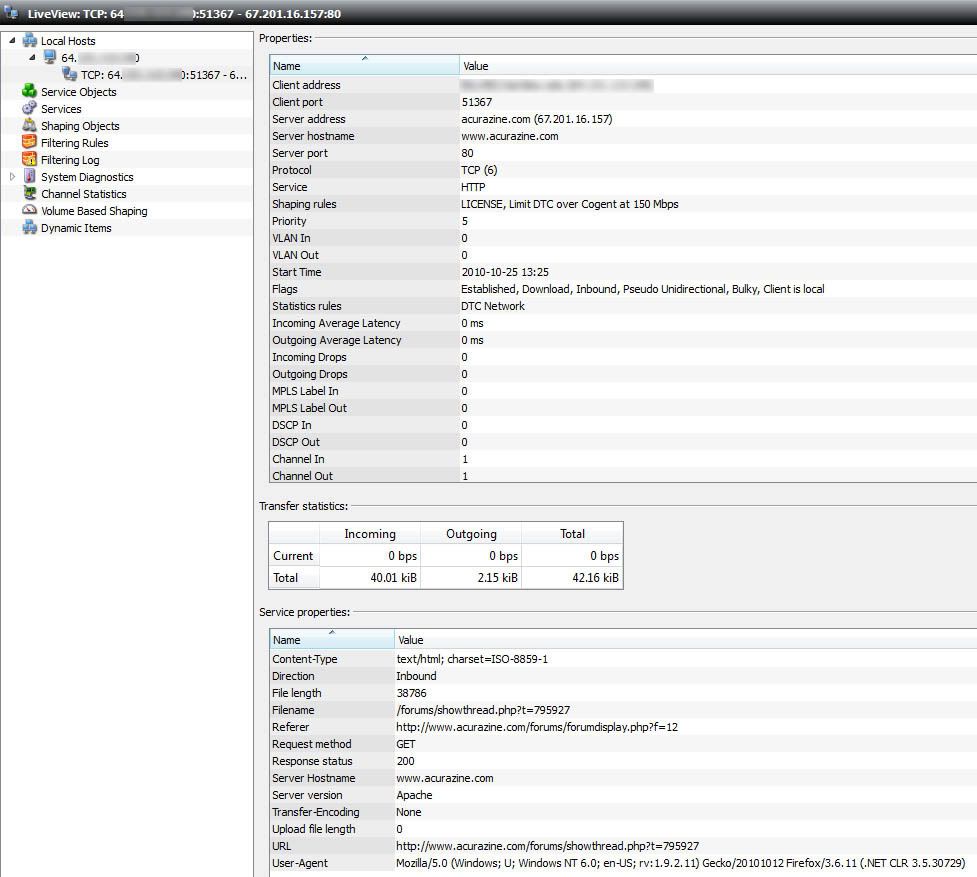
As an example of what's possible, I pointed one our recent acquisitions here at work at my own machine while viewing this thread. This is the sort of detail that modern network management systems let you drill down to.
In my case, this is a bandwidth management system. It only shows you this level of detail in a "live view" mode so that you can see what an end user station is doing if they appear to be hogging bandwidth. Nothing is permanently recorded besides bandwidth totals and the general category the traffic is categorized with. There are several other systems out there that record everything at this level of detail in the screenshot.
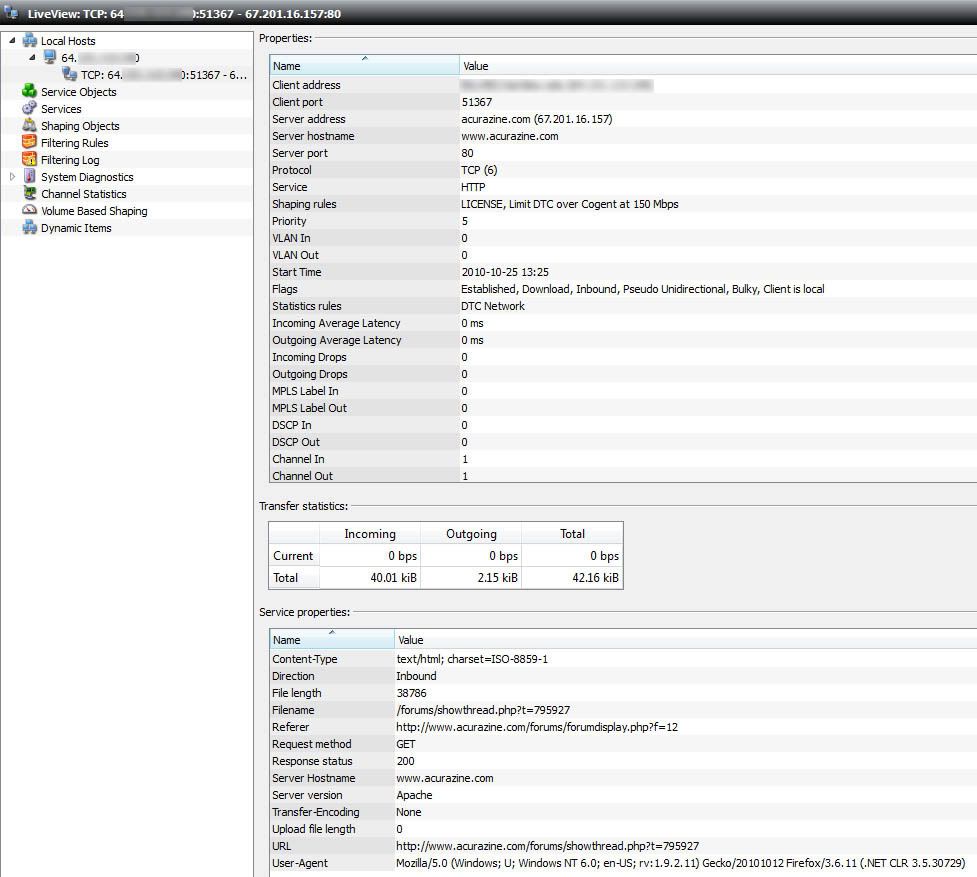
In my case, this is a bandwidth management system. It only shows you this level of detail in a "live view" mode so that you can see what an end user station is doing if they appear to be hogging bandwidth. Nothing is permanently recorded besides bandwidth totals and the general category the traffic is categorized with. There are several other systems out there that record everything at this level of detail in the screenshot.
#39
#40
well im up and using hotspotshield, having no trouble, but I didnt know it would give me this ad-bar at the top of every web page.  not a BIG deal, you can X it out - but then it comes again if you go to another page. not a big price to pay for anonymous browsing, but I wonder what my browsing looks like on the logs? anyone know?
not a BIG deal, you can X it out - but then it comes again if you go to another page. not a big price to pay for anonymous browsing, but I wonder what my browsing looks like on the logs? anyone know?
 not a BIG deal, you can X it out - but then it comes again if you go to another page. not a big price to pay for anonymous browsing, but I wonder what my browsing looks like on the logs? anyone know?
not a BIG deal, you can X it out - but then it comes again if you go to another page. not a big price to pay for anonymous browsing, but I wonder what my browsing looks like on the logs? anyone know?





